Secure and Reliable Information Administration Through Cloud Provider
In the ever-evolving landscape of data administration, the usage of cloud solutions has arised as an essential service for organizations looking for to strengthen their data protection measures while streamlining operational effectiveness. universal cloud Service. The detailed interaction in between safeguarding sensitive information and making sure seamless ease of access presents a complicated difficulty that companies should browse with persistance. By checking out the nuances of safe data monitoring via cloud solutions, a deeper understanding of the strategies and modern technologies underpinning this paradigm change can be introduced, dropping light on the multifaceted benefits and factors to consider that form the modern data management environment
Value of Cloud Providers for Data Monitoring
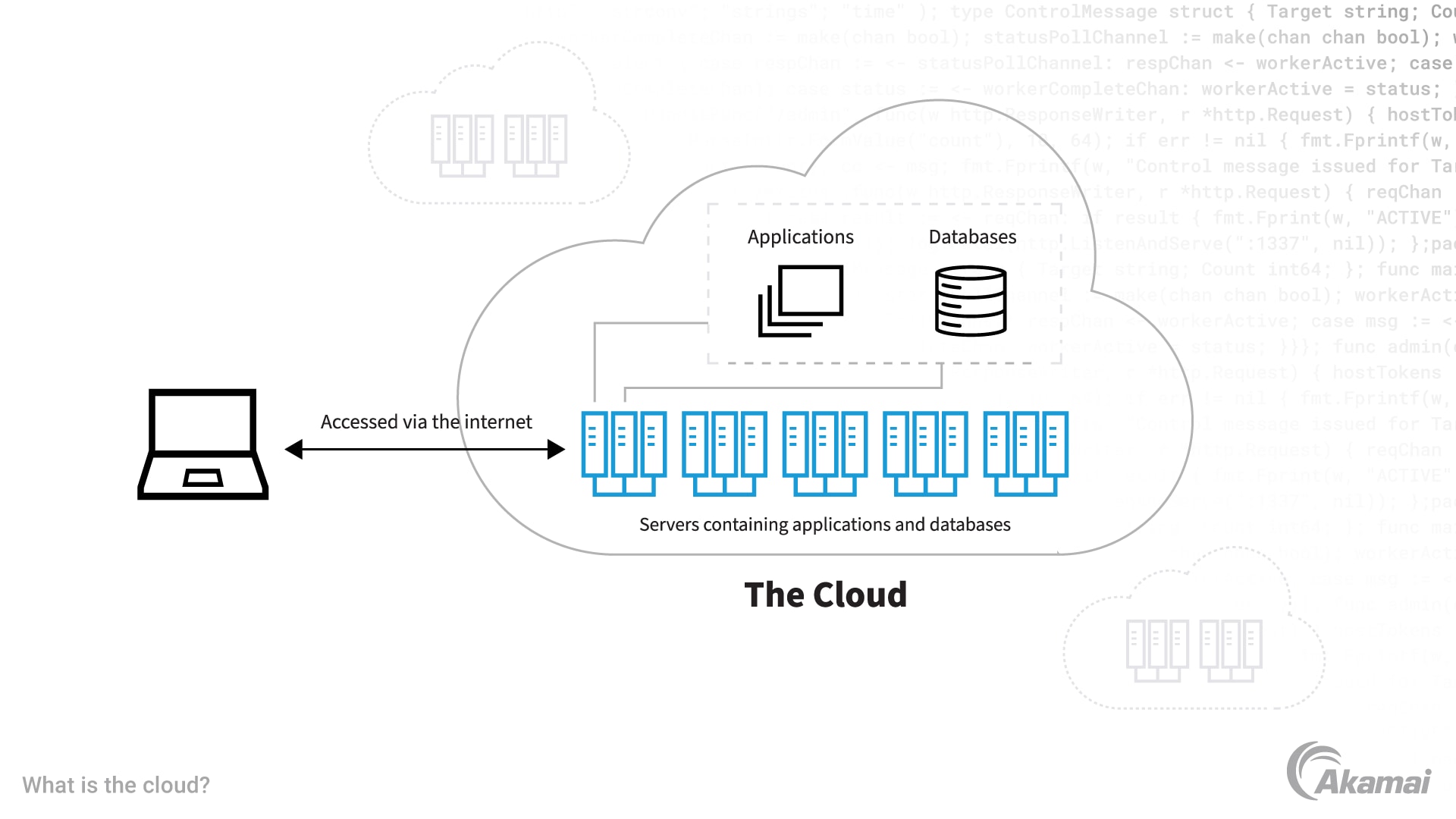
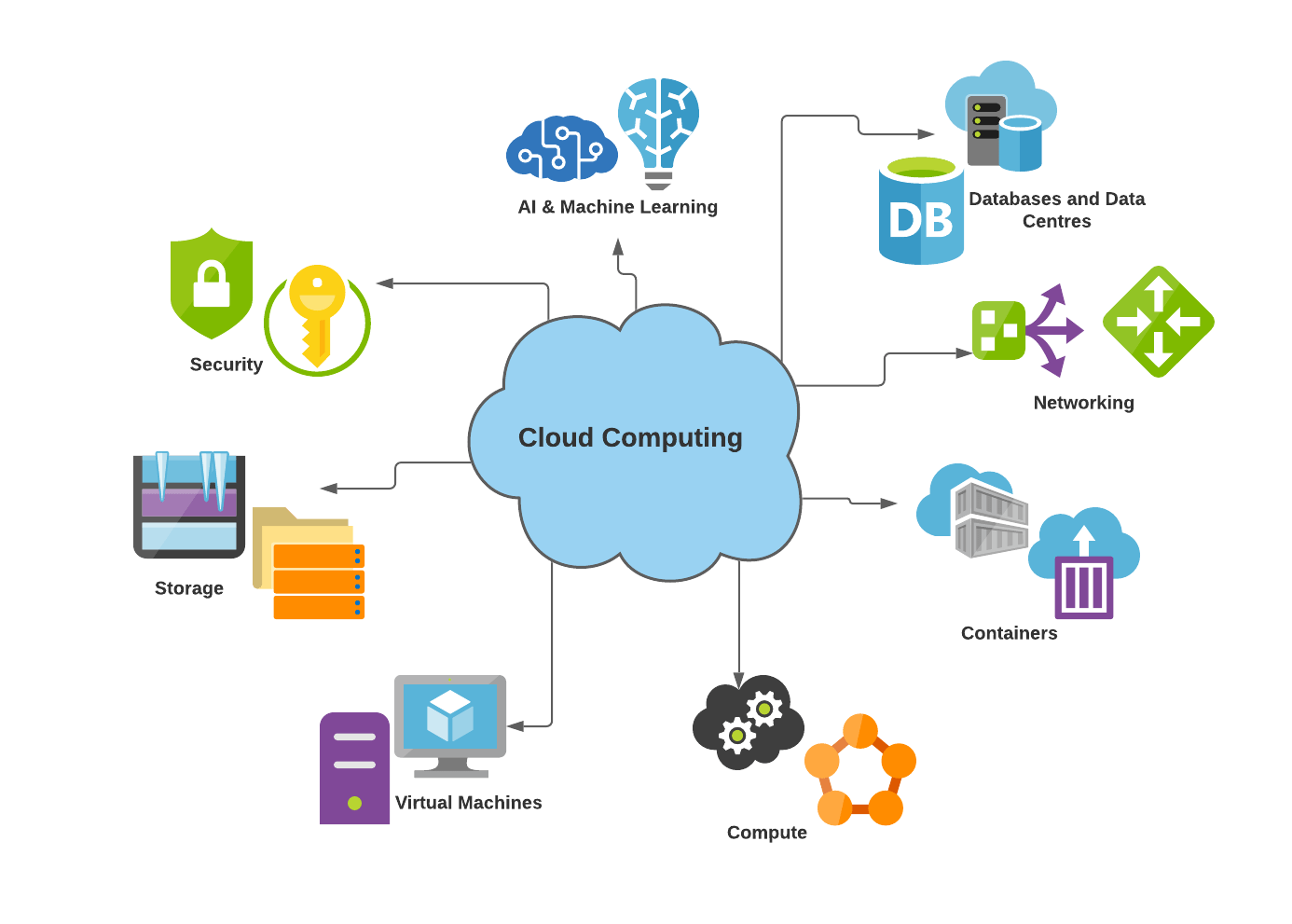
Cloud services play an essential duty in modern data management practices due to their accessibility, scalability, and cost-effectiveness. In addition, cloud services supply high ease of access, enabling customers to access data from anywhere with a net link.
In addition, cloud services provide cost-effectiveness by eliminating the requirement for investing in pricey equipment and maintenance. Organizations can choose subscription-based designs that align with their budget and pay only for the sources they use. This assists in decreasing ahead of time costs and general functional costs, making cloud solutions a feasible option for companies of all sizes. Essentially, the value of cloud solutions in information monitoring can not be overemphasized, as they give the necessary tools to streamline operations, enhance cooperation, and drive organization development.
Trick Security Obstacles in Cloud Information Storage
To deal with these safety challenges, companies need robust security actions, consisting of file encryption, gain access to controls, regular protection audits, and personnel training. Partnering with relied on cloud company that provide innovative safety and security features and conformity qualifications can likewise aid alleviate dangers connected with cloud data storage space. Ultimately, a positive and comprehensive approach to protection is vital in safeguarding data saved in the cloud.
Implementing Data Security in Cloud Solutions
Carrying out information encryption in cloud options entails utilizing durable encryption formulas and protected vital administration methods. Security secrets need to be stored individually from the encrypted information to include an extra layer of protection. Furthermore, companies must regularly update encryption keys and utilize solid accessibility controls to limit that can decrypt the information.
Furthermore, information encryption should be applied not only throughout storage yet likewise throughout data transmission to and from the cloud. Safe and secure communication protocols like SSL/TLS can assist safeguard information in transportation, making sure end-to-end security. By focusing on information security in cloud remedies, companies can bolster their data safety stance and keep the privacy and stability of their sensitive info.
Finest Practices for Data Backup and Recovery
Moreover, performing regular healing drills is vital to test the performance of backup treatments and the organization's capacity to restore information swiftly. File encryption of backed-up information adds an additional layer of security, safeguarding sensitive info from unauthorized access throughout storage space and transmission.
Tracking and Auditing Information Access in Cloud
To preserve information honesty and safety within cloud settings, it is critical for organizations to establish durable investigate this site actions for surveillance and auditing data access. Tracking information gain access to involves tracking who accesses the information, when they do so, and what activities they perform. By executing monitoring mechanisms, organizations can find any kind of unapproved accessibility or uncommon tasks promptly, enabling them to take immediate action to reduce potential dangers. Auditing data access goes a step even more by offering an in-depth document of all information accessibility tasks. This audit path is crucial for compliance click this objectives, examinations, and identifying any kind of patterns of dubious actions. Cloud provider often supply devices and solutions that promote monitoring and bookkeeping of information access, permitting organizations to gain understandings right into exactly how their data is being utilized and making certain liability. universal cloud Service. By proactively monitoring and bookkeeping information access in the cloud, companies can enhance their general safety and security stance and maintain control over their sensitive info.
Verdict
In final thought, cloud solutions play a crucial function in making certain effective and safe and secure data management for organizations. By addressing essential security difficulties via information encryption, backup, healing, and checking methods, companies can protect sensitive info from unapproved accessibility and data violations. Implementing these finest techniques in cloud solutions promotes data stability, discretion, and ease of access, eventually enhancing cooperation and performance within the company.
The crucial safety obstacles in cloud information storage space rotate around information violations, information loss, compliance policies, and data residency issues. By encrypting data before it is uploaded to the cloud, organizations can alleviate the threat of unapproved gain access to and data breaches. By prioritizing data file encryption in look here cloud services, organizations can bolster their data security stance and maintain the confidentiality and integrity of their delicate details.
To preserve data integrity and safety and security within cloud atmospheres, it is important for organizations to establish durable procedures for tracking and auditing data accessibility. Cloud service companies often use tools and services that facilitate tracking and bookkeeping of information access, permitting organizations to obtain understandings right into how their information is being used and making sure accountability.